If you are in an online business for a while, you must have
dealt with different types of spam at some point or another. However, if you
are just starting, you must have many things to learn for enhanced protection.
So, here we will learn about differe...
If you are in an online business for a while, you must have
dealt with different types of spam at some point or another. However, if you
are just starting, you must have many things to learn for enhanced protection.
So, here we will learn about different types of spam to know
more about things in this regard:
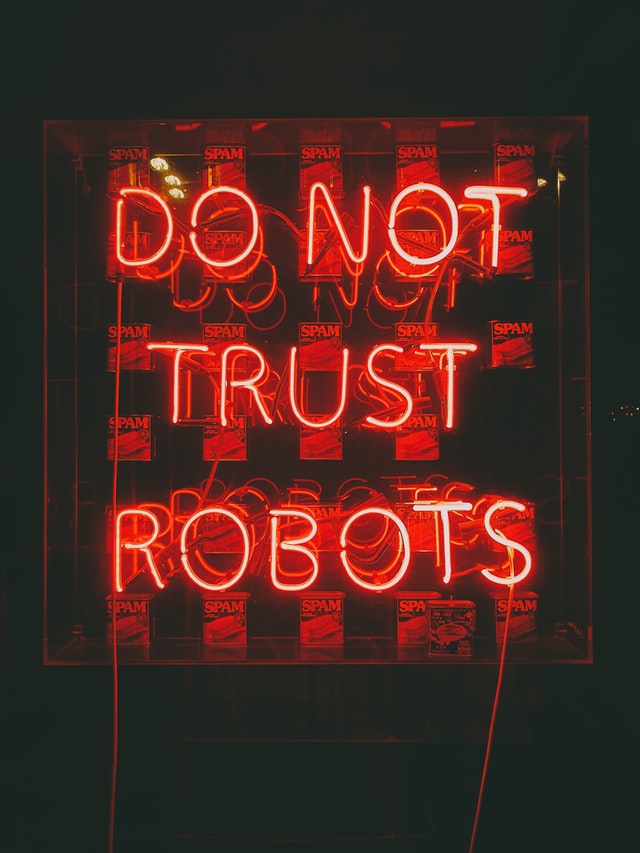
What Is Spam?
Spams are irrelevant and unsolicited messages sent over the
internet, generally to a large number of people, to spread malware, phishing,
or even advertising.
At present various things are considered spam, from blasting
comments to sending emails.
How to protect yourself from spam?
Here are some ways you can consider to protect yourself from
spam:
Firstly, make sure to download anti-virus or spam-filtering
tools to scan the links, emails, or other things you find over the internet.
These will help you prevent from opening that. Ultimately, you can reduce the
chances of clicking sources containing malware.
Avoid clicking on any suspicious links..
Full article: https://protectumus.com/blog/details/website-spam-...